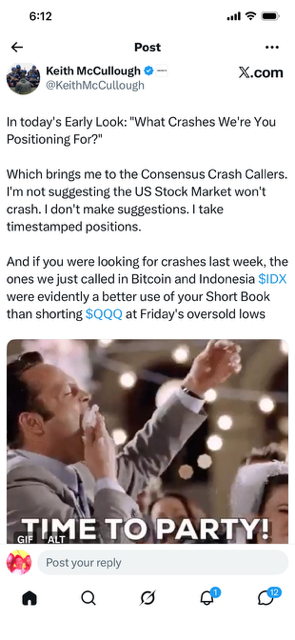
• Keith McCullough critiques “Consensus Crash Callers” for focusing on a potential US stock market crash while highlighting better-timed short positions his team called last week in Bitcoin and Indonesia’s IDX index.
• He stresses his method of taking timestamped trading positions rather than issuing vague predictions or suggestions about market direction.
 • The post from his “Early Look” includes a celebratory “TIME TO PARTY!” GIF, underscoring ironic contrast to poorly positioned QQQ shorts at Friday’s oversold lows.
• The post from his “Early Look” includes a celebratory “TIME TO PARTY!” GIF, underscoring ironic contrast to poorly positioned QQQ shorts at Friday’s oversold lows.
{ 0 comments }





 Duck9 is a credit score prep program that is like a Kaplan or Princeton Review test preparation service. We don't teach beating the SAT, but we do get you to a higher credit FICO score using secret methods that have gotten us on TV, Congress and newspaper articles. Say hi or check out some of our free resources before you pay for a thing. You can also text the CEO:
Duck9 is a credit score prep program that is like a Kaplan or Princeton Review test preparation service. We don't teach beating the SAT, but we do get you to a higher credit FICO score using secret methods that have gotten us on TV, Congress and newspaper articles. Say hi or check out some of our free resources before you pay for a thing. You can also text the CEO: